Vulnerabilities
Latest Dynatrace
Vulnerabilities  provides a unified overview of third-party, code-level, and runtime vulnerabilities detected in your environments monitored by Dynatrace. It helps you prioritize vulnerabilities based on valuable insights and context needed to analyze the impact and efficiently address remediation actions.
provides a unified overview of third-party, code-level, and runtime vulnerabilities detected in your environments monitored by Dynatrace. It helps you prioritize vulnerabilities based on valuable insights and context needed to analyze the impact and efficiently address remediation actions.
Try Vulnerabilities  and share your feedback to help us improve.
and share your feedback to help us improve.
Capabilities
- Prioritize third-party, code-level, and runtime vulnerabilities based on Davis Security Score, which combines CVSS with observability context.
- Control the displayed data based on filtering and formatting options according to your points of interest.
- Understand what is at risk and why: view affected processes, related services, applications, and hosts, as well as Kubernetes workloads, nodes, and clusters.
- Zoom into vulnerabilities based on a specific risk vector: are affected entities accessible from the public internet or connected to data assets? Is there a public exploit available?
- Optimize remediation activities using recommendations from Davis Security Advisor: determine which patches and upgrades to apply for maximum remediation impact.
- Ignore vulnerabilities that are less important and focus on what matters.
- Address and monitor remediation: connect remediable entities to your ticketing system and follow the remediation progress.
- Drive automation use cases and access security findings with Grail.
- Share results of your findings with developers and stakeholders.
Prerequisites
Permissions
For a list of permissions required, go to Dynatrace Hub  , select Vulnerabilities, and display Technical information > User permissions.
, select Vulnerabilities, and display Technical information > User permissions.
Get started
For installation instructions, see Dynatrace Hub: Install.
Once you open Vulnerabilities  , you can take the following actions to address vulnerabilities:
, you can take the following actions to address vulnerabilities:
Format table 
Select which information is to be displayed in the vulnerabilities or remediable entities table:
Filter by relevant info 
Cut through the plethora of vulnerabilities and filter for what you're looking for. Using the filter bar, you have the following filter options:
Filter by DSA fixes 
Third-party vulnerabilities
Filter the vulnerabilities table by recommended fixes from Davis Security Advisor (DSA).
-
On the Prioritization page, on the upper-left of the vulnerabilities table, select
Davis Security Advisor. This opens a Davis Security Advisor side window with a list of recommendations.
-
Select
for the desired library. This filters the vulnerabilities table by the total number of vulnerabilities for a selected library that would be fixed by upgrading the library.
You can add as many DSA filters as you want.
- To remove a filter, select Clear next to the desired library.
- To remove all filters and return to the previous state of the vulnerabilities table, select Clear all.
The Create report and Open with functions aren't available if DSA filters are set. Remove your filters to perform these actions (select 
Create a report 
Convert data from the vulnerabilities table into a DQL query that can be opened in Dashboards or Notebooks via available options (use ready-to-use templates or build your own dashboard or notebook).
Results are displayed based on your selected filters.
On the Prioritization page, on the upper part of the vulnerabilities table, select 
- Use template: Opens the results in our predefined Third-party vulnerabilities exposure report template.
- Build dashboard/notebook: Opens the resulting DQL query in a new or existing dashboard or notebook, allowing you to build on it.
For information on Davis Security Score calculations on Grail-powered apps, see Calculation differences.
Open with 
Open the data from the vulnerabilities table in another app. Results are displayed based on your selected filters.
On the Prioritization page, on the upper part of the vulnerabilities table, select 
For information on Davis Security Score calculations on Grail-powered apps, see Calculation differences.
Download as CSV 
Download data in the vulnerabilities table as a CSV file.
- On the Prioritization page, on the upper-right of the vulnerabilities table, select
.
- Select Download as CSV.
Select one of the available options:
-
All: Download all result pages in the table.
-
Current page: Download current result page in the table.
-
Selected: Download selected vulnerabilities in the table (you first need to select the checkboxes next to the desired vulnerabilities).
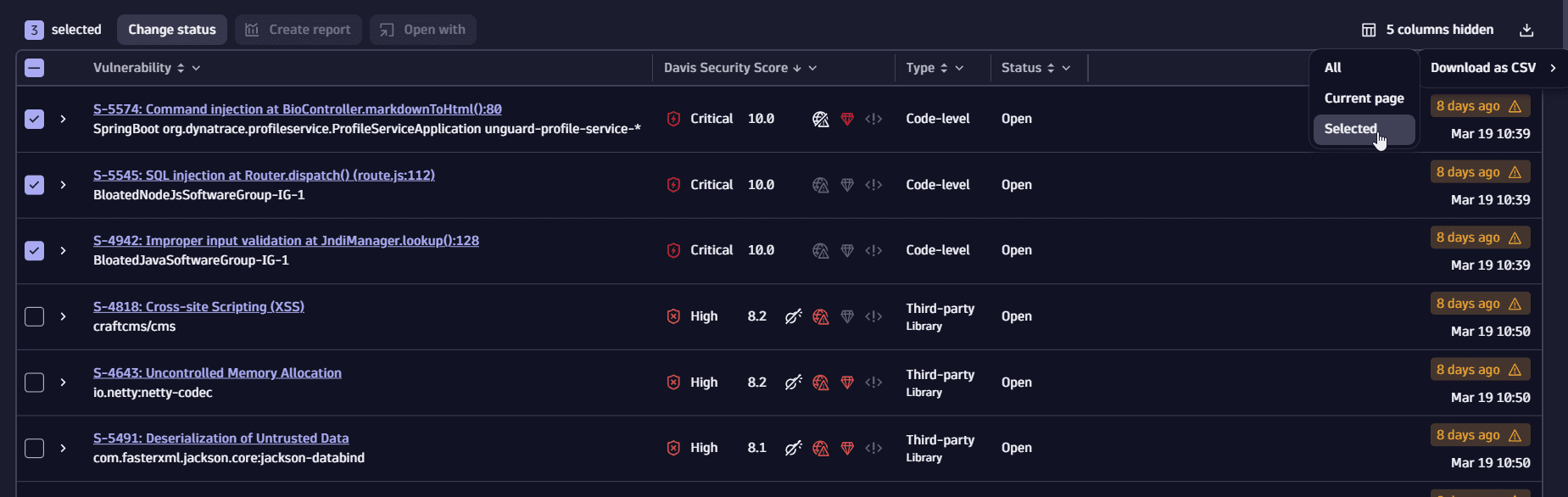
Risk assessment can't be exported.
Change status 

Mute (silence) or unmute vulnerabilities according to your findings and needs. For example, you can mute an open vulnerability if you don't consider it important, mute a resolved vulnerability to stop monitoring it if it's reopened, or unmute a vulnerability that turns out to be important.
Muted vulnerabilities don't appear in the vulnerabilities table unless you filter for them.
For third-party vulnerabilities, you can also mute or unmute remediable entities. See below for details.
-
Mute or unmute vulnerabilities
-
Mute or unmute remediable entities
Third-party vulnerabilities
Track remediation
Third-party vulnerabilities
Navigate to the overview page of the remediable entities (the related and affected entities associated to a vulnerability) and track their remediation progress.
The fastest way is from the Prioritization page: expand a row for a selected vulnerability, then select View all process groups/View all Kubernetes nodes.
Set tracking links
Third-party vulnerabilities
Add links to tickets created in your issue tracking system for the affected entities to track the remediation progress of remediable entities. Adding a tracking link allows you to navigate to the associated URL. You can easily check, for example, if someone is already working on fixing the vulnerability.
Navigate to the overview page of the remediable entities. There, you have several options to add, edit, or delete tracking links individually or in bulk, as described below.
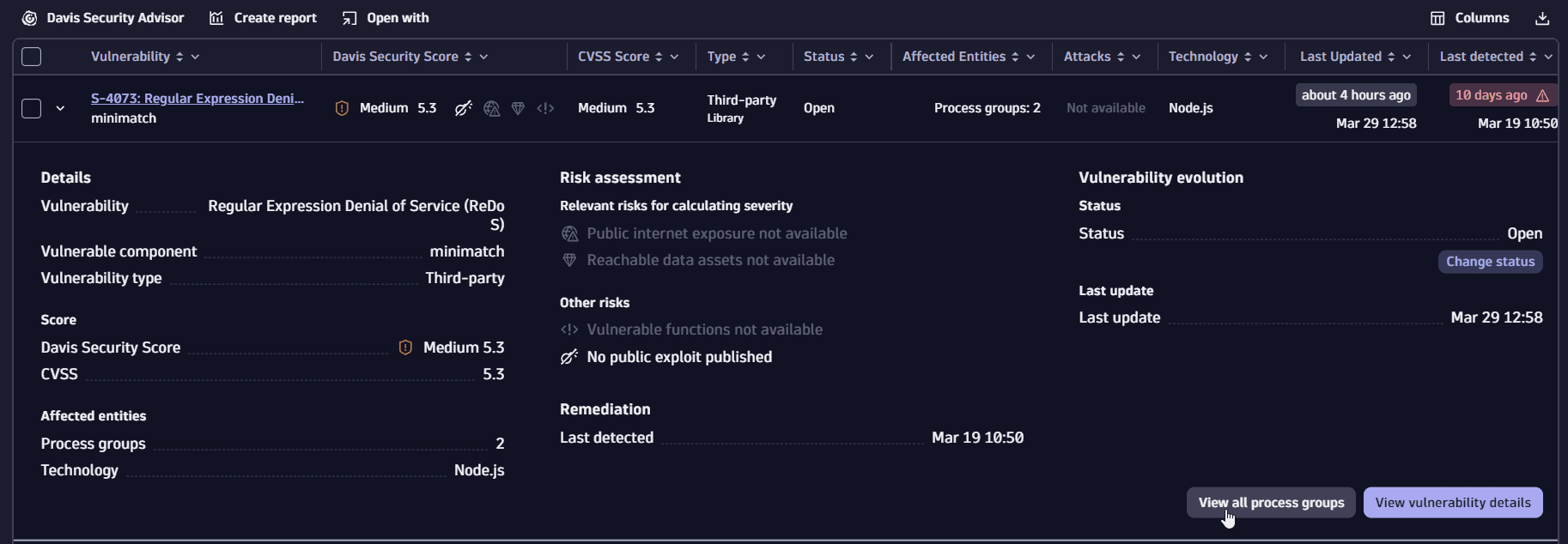
Peek at the relevant info
Peek at the relevant information while browsing through the vulnerabilities table without navigating to the details page of a vulnerability.
Dive into details
Explore the most essential data on the details page of a vulnerability. This provides you the context needed to analyze the impact and address remediation actions. For details, see Concepts.
The fastest way is on the Prioritization page: select a vulnerability title.
Explore functionalities
Functionalities based on which you can evaluate vulnerabilities are described below.
Vulnerability status
The resolution and mute status of a vulnerability or remediable entity. Potential states are:
-
Open: The vulnerability or remediable entity is active. -
Resolved: The vulnerability or remediable entity was closed automatically because the root cause is no longer present. For details, see Vulnerability evaluation: Resolution. -
Muted (Open): The vulnerability or remediable entity is active but was silenced by request. -
Muted (Resolved): The silenced active vulnerability or remediable entity was closed automatically because the root cause is no longer present.A muted vulnerability or remediable entity that was closed automatically doesn't change its status to
Resolved, but toMuted (Resolved).
To change the status of vulnerabilities or remediation entities, see Change status.
Davis Security Score (DSS)
Davis Security Advisor (DSA) 
Third-party vulnerabilities
Davis Security Advisor recommends fixes consisting of library updates in the monitored technologies.
It also determines
How many vulnerabilities you can solve by updating a specific library
How many of the total solvable vulnerabilities are the most severe
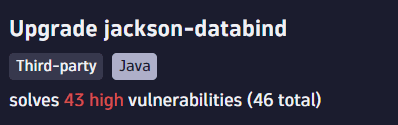
To filter by recommended fixes, see Filter by DSA fixes.
To learn how DSA calculates recommended fixes, see FAQ: How does Davis Security Advisor calculate recommended fixes?.
Public internet exposure 
One of the risk assessment factors taken into consideration when determining the Davis Security Score. If there is public internet exposure it means that vulnerabilities affect at least one process that is exposed to the internet. To find out how Dynatrace determines public internet exposure, see FAQ: How is public internet exposure determined?.
Possible states are:
- Public network: There is public internet exposure.
- Not detected: No public internet exposure was found.
- Not available: Data isn't available, because the related hosts are running in Infrastructure Monitoring mode. For details, see Monitoring modes.
Reachable data assets 
One of the risk assessment factors taken to consideration when determining the Davis Security Score. If there are any reachable data assets affected it means that vulnerabilities affect at least one process that has database access (runs a database service).
Possible states are:
- Within range: There are reachable data assets affected.
- None within range: There are no reachable data assets within range.
- Not available: Data isn't available, because the related hosts are running in Infrastructure Monitoring mode. For details, see Monitoring modes.
Reachable data assets is displayed on the details page of a vulnerability, and
Provides information about the last five database services accessed by affected processes containing the identified vulnerability
Allows you to track the reachable databases directly connected to a vulnerability
Vulnerable functions 
Third-party vulnerabilities
One of the risk factors to be considered when assessing a vulnerability. If there are any vulnerable functions in use, then there is at least one process using a vulnerable function (this might indicate a higher exploitation risk). Possible states are:
- In use: There are vulnerable functions in use.
- Not in use: No vulnerable functions in use were found.
- Not available: Data isn't available.
Vulnerable functions is displayed on the details page of a vulnerability in Vulnerability details and provides the following information.
| Attribute | Description | Example |
|---|---|---|
| Class | The class that contains the vulnerable function related to the vulnerability. | org.apache.http.client.utils.URIUtils |
| Vulnerable function | The function related to the vulnerability. | validateSubType |
| Function usage | Shows whether the vulnerable function is being used by your application. Based on whether your application uses the vulnerable function, you can assess the impact on your environment. The usage of a vulnerable function is calculated on the process level and is aggregated to the process group level, which results in a count of affected process groups per function. | In use, Not in use, Not available |
| PGs | A count of the related process groups based on the function usage. If there are process groups that are affected by the vulnerability (use at least one vulnerable function), you can select the number to navigate to the remediation tracking for the respective process groups. | 2 |
To find out how vulnerable functions are determined, see FAQ: How are vulnerable functions determined?.
Public exploit 
Third-party vulnerabilities
One of the risk factors to be considered when assessing a vulnerability. If there is any public exploit published it means that malicious code to exploit this vulnerability is available on the internet.
Possible states are:
- Public exploit published: A publicly-known exploit for this vulnerability is available.
- No public exploit published: No publicly-known exploit for this vulnerability is available.
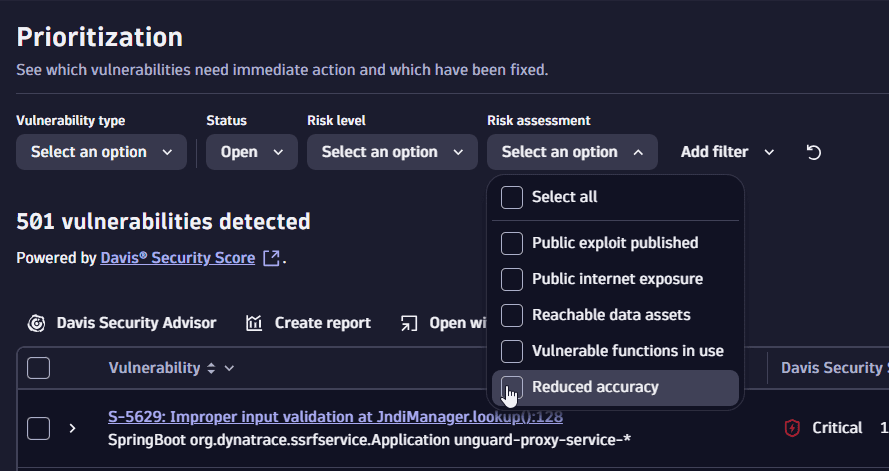
Reduced accuracy
Reduced accuracy means there are vulnerabilities with related hosts running in Infrastructure Monitoring mode or OneAgent Discovery mode, for which detailed analysis is not possible.
How this affects the DSS calculation: The context of internet exposure or reachable data assets cannot be examined due to the lack of information, thus the DSS score can't be lowered. For more information, see Monitoring modes.
When Full-Stack Monitoring isn't enabled, an alert is displayed on the details page of a vulnerability.
On the Prioritization page, in the filter bar, filter for Risk assessment > Reduced accuracy.
Process group/Kubernetes node overview
Third-party vulnerabilities
Related entities
Related entities are entities that are connected to one of the affected entities, thus indirectly affected by the vulnerability. See below which entities can be related to a vulnerability and how you can track them down.
| Attribute | Description | How to track down |
|---|---|---|
| Related process group/Kubernetes node Third-party vulnerabilities | A process group or Kubernetes node that is related to an affected entity. | To track down, see Process group/Kubernetes node overview. You can also set tracking links and track remediation progress. |
| Related application | An application that calls a vulnerable service, or an application that calls a non-vulnerable service that calls a vulnerable service. | On the details page of a vulnerability in Related entities. |
| Related service | A service that runs directly on a vulnerable process group instance. | On the details page of a vulnerability in Related entities. |
| Related host | A host on which the vulnerable process runs. | On the details page of a vulnerability in Related entities. |
| Related database | A database that is accessed by the vulnerable process or reachable from it. | On the details page of a vulnerability in Related entities. |
| Related Kubernetes workload | In Kubernetes environments, the workload to which the vulnerable process belongs. | On the details page of a vulnerability in Related entities. |
| Related Kubernetes cluster | In Kubernetes environments, the cluster to which the vulnerable process belongs. | On the details page of a vulnerability in Related entities. |
| Related container image Third-party vulnerabilities | In Kubernetes environments, the container image used by the affected processes. | On the details page of a vulnerability in Related container images (if containers are detected). |
Affected entities
To fix vulnerabilities, you need to address affected entities. Affected entities are entities (process groups, processes, and Kubernetes nodes) for which a vulnerability was detected, and are therefore directly affected by the vulnerability.
Details about affected entities are available in multiple places:
- On the Prioritization page (format the vulnerabilities table by Affected entities, or expand a row for a selected vulnerability)
- Third-party vulnerabilities On the details page of a vulnerability, in Process group/Kubernetes node overview
- Third-party vulnerabilities On the overview page of the remediable entities
Vulnerable components
Third-party vulnerabilities
Vulnerable components provides information about the name and description of the libraries containing the identified vulnerability and the number of affected processes and is displayed on the details page of a vulnerability.
A vulnerable component is a software component (library) or runtime component (for example, a Kubernetes package) that has a vulnerable function causing a vulnerability:
- For Snyk-based vulnerabilities, the package name (example:
org.apache.tomcat:tomcat-coyote) - For NVD-based vulnerabilities, the runtime technology (examples:
Java runtime,Node.js runtime)
To determine how Dynatrace evaluates vulnerable components, see Vulnerability evaluation: Third-party vulnerabilities.
Entry points
Code-level vulnerabilities
Entry points allows you to go to the source of the vulnerability to determine in which ways it could be exploited and is displayed on the details page of a code-level vulnerability.
An entry point is a point in the code where an attacker could enter the application and exploit a vulnerability, for example, by passing user input fields to the application (such as a login form or search bar). To evaluate a code-level vulnerability, the following entry point information is provided:
| Attribute | Description | Example |
|---|---|---|
| URL path | The path used in the HTTP request to reach and potentially exploit the vulnerability. | /user/1218/bio |
| Untrusted inputs | The number of inputs that are passed to the usage. | 1 |
| Payloads | The user-controlled inputs that could be used to exploit the vulnerability. If there's a key for the payload (for example, an HTTP parameter name or an HTTP header name), it's displayed after the colon. | HTTP parameter value: bioText |
| SQL statement | In an SQL injection, the vulnerable input (the SQL statement). The user-controlled input is highlighted. | 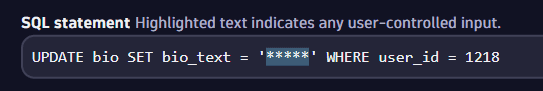 |
| Command | In a command injection, the vulnerable input (the command used). The user-controlled input is highlighted. | 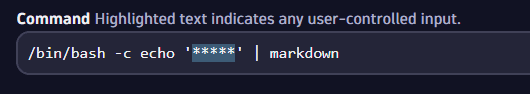 |
| Improperly validated input | In a JNDI injection, the vulnerable input (the improperly validated input). The user-controlled input is highlighted. |  |
If the same vulnerability is reachable by multiple HTTP paths, multiple entry point entries are listed. To save memory and network traffic, a limited number of entries is displayed.
If a code-level vulnerability is resolved or is about to be resolved in the next 30 minutes, the entry points are no longer open (vulnerable).
Code location
Code-level vulnerabilities
Code location reflects the location where the vulnerable function is called from (for example, SQL injection at DatabaseManager.updateBio():82).
Code location is displayed
- On the Prioritization page (expand a row for a selected vulnerability)
- On the details page of a vulnerability in Vulnerability details
Vulnerability evolution
Vulnerability evolution provides a better understanding of the evolution of a vulnerability over time based on current status and the latest events. It's displayed on the details page of a vulnerability.
Events are stored for one year.
Limitations
Timeframe selection is currently not available.
Navigation to affected and related processes is currently not available.